ZyLAB is happy to announce the achievement of SOC2 Type I certification. This is an important milestone in ZyLAB’s Security roadmap and a continuous reassurance to our customers we hold security as a first class citizen within ZyLAB.
ZyLAB has been operating in compliance to the SOC2 requirements for the past few years and now that compliance has been validated by a certified external organization. SOC2 ensures ZyLAB can securely manage customer data and protect the interests and privacy of their customer’s organizations.
ZyLAB is active in the truth finding arena (eDiscovery), which requires ZyLAB not only to produce secure software, but also to operate a secure SaaS platform. Customers need a high level of security for their information being processed via ZyLAB ONE, so both the software and the SaaS platform need to be secure in the broadest meaning of the word.
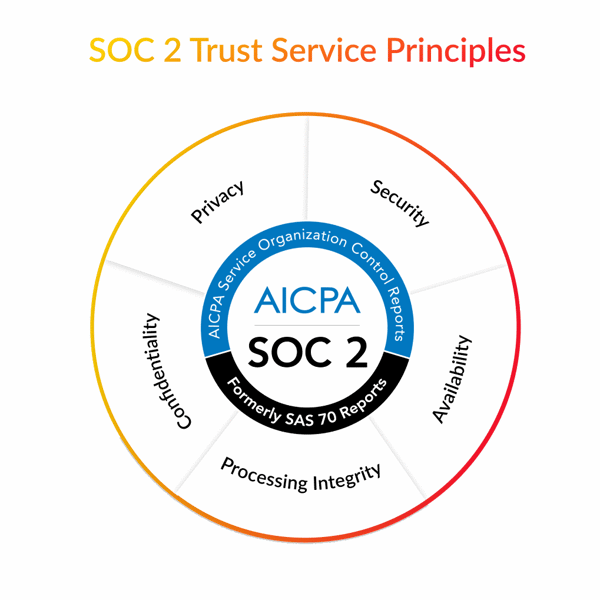
To support ZyLAB’s mission and vision, the SOC2 service commitments are defined to include the full scope of the SOC2 framework: Security, Confidentiality, Availability, Processing Integrity and Privacy.
What exactly is SOC2?
SOC2 is one of the most sought after standards in security and compliance. It represents the highest degree of excellence in systems and operations control. SOC stands for Service Organization Control, and was developed by the American Institute of CPAs (AICPA). SOC2 is specifically designed for service providers storing customer data in the cloud.
SOC2 requires companies to establish and enforce strict information security policies and procedures. The criteria for developing these policies and procedures is based on five “trust service principles”:
- Security – is the system protected, both physically and logically, against unauthorized access?
- Availability – is the system available for operation and use as agreed upon?
- Confidentiality – is the information that’s designated as confidential protected as agreed upon?
- Processing Integrity – are the processing services provided in a complete, accurate, and timely, manner?
- Privacy – is personal information collected, used, retained, disclosed, and destroyed in accordance with the service organization’s privacy notice and business objectives?
The Security principle includes the so-called common criteria which are categorized based on the following:
|
|
 The SOC2 Certification Process
The SOC2 Certification Process
SOC2 certification requires the adoption of policies and procedures for protecting information in areas including human resources, physical security, software development, operational security, business continuity, access management, asset management, vendor management, etc. To be certified, a company must evaluate all their people, processes, and IT systems and systematically apply risk management processes to each.
In order to examine ZyLAB’s security standards and operations, an external certified auditing entity was needed to ensure ZyLAB ONE is compliant and follow best practices. For this, we selected 2-Control as our auditors to achieve SOC2 certification.
With 2-Control, we have performed a thorough and detailed analysis of the existing security standards of ZyLAB, and worked tirelessly to meet the requirements of the SOC2 framework. The entire SOC2 criteria (Trust Service Principals) was scoped for the audit. Every criterion holds dozens of controls and measures, and each should be checked against security practices within ZyLAB. Simply maintaining security practices isn’t enough- you have to make sure that each security measure is well-documented and its performance is evaluated.
To analyse each control, and fine tune or extend our current security standards to meet the SOC2 certification requirements, ZyLAB established a cross functional team. Once this was completed, everything was verified by 2-Control during a 3 day hands-on audit which included interview sessions, hundreds of questions, hands-on sessions evaluating evidence that the right standards and procedures are in place and followed. The result of that audit is a detailed SOC2 report illustrating ZyLAB’s security standards, as well as a description of its systems and operations..
The components of a SOC 2 report include:
- Independent Service Auditor’s Report – containing a description of the service auditor’s examination of the suitability and effectiveness of the controls to meet the Trust Services Criteria.
- Assertion – containing a description for users of the service organization’s system controls, intended to meet Trust Services Criteria.
- System Overview – providing background information on the service organization of the software, people, procedures, and data within the organization’s environment.
- Relevant Aspects of Controls – providing a description on the control environment, the risk assessment process, information communication systems, and monitoring of controls.
- Trust Services Criteria, Related Controls, and Tests of Controls – outlining the controls in place and describing the tests on the effectiveness of the controls to meet the Trust Services Criteria.
- Other Information provided by the Service Organization
Asked to comment on ZyLAB's certification process, the auditor provided the following comment:
“To prepare an organization for the first time to be SOC2 compliant is a very intensive process and requires the whole organization to be involved. At Zylab, we experienced a professional and committed approach to this process. We congratulate Zylab with the results of their efforts!”
Rogier Haest, IT-Auditor, 2-Control
Why SOC2 matters for eDiscovery
Businesses and law firms use eDiscovery technology to manage massive amounts of data during critical legal and business-oriented processes. These processes include litigation, arbitration, responding to subpoenas and regulatory requests, monitoring compliance, preparing virtual data rooms, and so on. Government agencies use eDiscovery for many of the same reasons as well as to help prepare responses to public records requests.
The data involved in these processes almost always contains significant amounts of private and confidential information. Information which, if exposed to the public or obtained by hackers, could cause catastrophic financial and reputational damage, as described above. A SOC2 certification establishes that an eDiscovery vendor has taken every possible precaution to address any and all potential security risks to ensure customer data is constantly and consistently protected.
Your security Matters to us
ZyLAB appreciates that customers place their trust in our company every day, and we believe we have a responsibility to manage and protect our customers’ information assets in exactly the same way as we protect our own.
The Management Team of ZyLAB takes this responsibility very seriously and is fully committed to comply with industry best practices in regards to information security, as shown by our overall Security strategy, and proven by our ISO27001 and SOC2 certifications among others.
Since 2017, ZyLAB’s policies, procedures and way of working have been formalized according to the ISO/IEC 27000 series. In November 2018, ZyLAB obtained the certification proving that it has successfully implemented an information security management system (ISMS) in accordance with ISO/IEC 27001:2013. Now, ZyLAB has also gained certification according to the SOC2 framework controls, proving advanced implementation of security standards.
For more information visit our trustcenter.